Look, I’m just as pissed off as you folks are that we will have to acknowledge “President Donald Trump” very, very soon. I didn’t want this. I didn’t want Hillary either, but frankly she’d have hurt a hell of a lot less. I don’t want him as my President, I don’t want him representing us to the rest of the world, and I sure as hell don’t want the world that he’ll help shape.
But…
There are violent protests going on all over the United States right now. That has to stop. It has to stop now, and never resume. You will fail, you will hurt those who are trying to keep the damage to a minimum. You will destroy the causes you want to support. And most importantly, you will help Trump prove his own misogynistic, homophobic, homicidal, dumb-ass, short-sighted, anti-humanity ideas.
That’s right, you are helping Donald Trump continue in his plans.
Look, there are a lot of ways that you can stand against him without destroying your own movement:
March and protest peacefully. Hell, we’ve overturned some very deep-rooted and immobile laws and feelings in this country with that policy. It works, and it works incredibly well.
VOTE! over 46% of those eligible to vote in this country failed to do so this year. Let’s say that half of those were unfairly not allowed to – a percentage that would be considered by even liberal sources to be high, but I’ll give you the benefit of the doubt. An additional 25% of the electorate participating would have absolutely changed the outcome. Maybe Trump would have still won, but at least there would have been one hell of a strong voice of opposition. Don’t stay home, don’t ignore the voting booth. Get out there and make your opinion count in the most powerful way the world has ever seen.
Finance organizations and volunteer. Planned Parenthood, Lambda Legal Defense Fund, The American Civil Liberties Union, there are a lot of them out there who are now under fire. Give them money. Give them time. They’re in desperate need of both, and that need is going to get more and more dire.
Stop those who would destroy your message. If you and your fellow marchers/protestors witness someone rioting or looting, surround them. Don’t put yourself in physical danger; just keep them from leaving the scene of a literal crime. Let the police in, and don’t let the criminals out. Force the news to report that those who stand in opposition to Trump will refuse to sanction violence and criminal behavior in their name, and force those who think this is appropriate behavior to recognize that it is not, and you will not either condone or assist them in it.
Finally, remember that Trump will be sworn in as president. We can’t stop that now. What we need to do is become what Britain calls “The Loyal Opposition.” Never let in or give up for a moment on your ideals or values. Never stop pushing (peacefully, effectively) against the policies you do not and can not endorse. But remember we are still all Americans. We are still all bound by the laws of our country and the leaders that are elected to make and uphold those laws. This isn’t a contradiction of terms or oxymoronic thinking, this is what our system of government was designed to do from the very beginning. Believe it or not, not everyone in Colonial America believed that secession and independence was the right idea. Some stood up in favor of remaining loyal to the crown. The did, however, still support the will of the people when the fledgling country decided on which direction it would move.
Teach people about the most powerful tools at our disposal to defeat bad laws: Peaceful Protest, Jury Nullification, Voting the morons out of office, the are a large number of them. Use them, teach others about them, but work within the system to change the system and the message will be broadcast to all the corners of the earth.
Riot and wreck up our cities, and not only is your own message lost, you support the very people you are trying to protest against.
We’re in this together. We will survive the next four years. Let’s not make the situation twenty times worse by fueling the very people and policies we stand against.
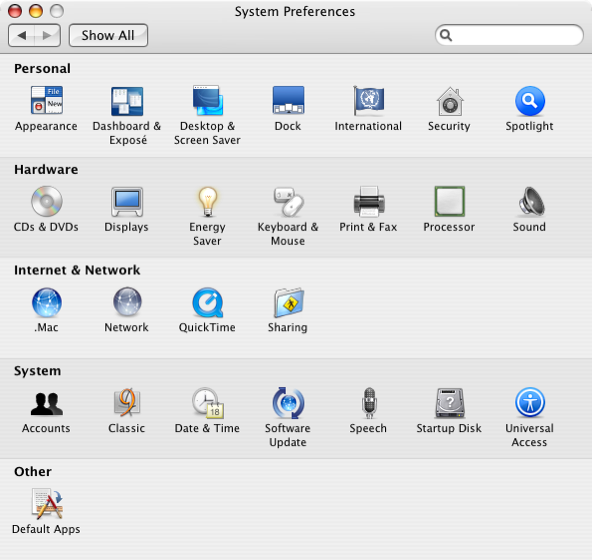 Usually, you can set default apps for certain file types right through OS X features directly. Email (in El Capitan) is done by going to the preference pane in Mail.app, most file types allow you to set the default by going to Get Info, etc. However, sometimes things go awry, and that’s where
Usually, you can set default apps for certain file types right through OS X features directly. Email (in El Capitan) is done by going to the preference pane in Mail.app, most file types allow you to set the default by going to Get Info, etc. However, sometimes things go awry, and that’s where  As you folks already know, I’m not totally immune from liking first or third party shooters. I loved Mass Effect (up until the ending of 3) and I’m nuts over the Fallout games. So when a new 3rd-Person shooter based in the aftermath of a massive disease outbreak and resulting loss of society came out, and it was based in New York City, I was in. The game, however, really and truly sucks for casual gamers, which became painfully obvious within about 90 minutes of playing. Here’s why:
As you folks already know, I’m not totally immune from liking first or third party shooters. I loved Mass Effect (up until the ending of 3) and I’m nuts over the Fallout games. So when a new 3rd-Person shooter based in the aftermath of a massive disease outbreak and resulting loss of society came out, and it was based in New York City, I was in. The game, however, really and truly sucks for casual gamers, which became painfully obvious within about 90 minutes of playing. Here’s why: Email is – for the most part – the stuff of modern productivity. Begin able to send and receive email, along with the calendars, contacts, and tasks that it brings; is essential to getting work done these days. When you use the native Mac apps, everything is fine. When you need to use 3rd-party tools, things go sideways in a hurry.
Email is – for the most part – the stuff of modern productivity. Begin able to send and receive email, along with the calendars, contacts, and tasks that it brings; is essential to getting work done these days. When you use the native Mac apps, everything is fine. When you need to use 3rd-party tools, things go sideways in a hurry. I was an early adopter of Amazon’s Prime Video service. They’ve offered tons of free content and a massive library of purchasable content for years now, and some time back the Amazon Streaming Video App for iPhone/iPad was released to allow folks to take the show on the road – literally. I’ve been a user of that app for about two years now, and the latest update brought a LOT to the table to make it even better.
I was an early adopter of Amazon’s Prime Video service. They’ve offered tons of free content and a massive library of purchasable content for years now, and some time back the Amazon Streaming Video App for iPhone/iPad was released to allow folks to take the show on the road – literally. I’ve been a user of that app for about two years now, and the latest update brought a LOT to the table to make it even better. OK, for the first time… well… ever… I have to actually agree with something that came out of Ben Shapiro’s mouth. This is not a comfortable situation.
OK, for the first time… well… ever… I have to actually agree with something that came out of Ben Shapiro’s mouth. This is not a comfortable situation. Jumping from one employer to another is never easy, but doing it after over a decade with your former employers can lead to some very interesting issues. Not the least of which, for me, is suddenly finding yourself in the very odd position of moving to knowing that people you’ve considered part of your work life for years and years are no longer “we.”
Jumping from one employer to another is never easy, but doing it after over a decade with your former employers can lead to some very interesting issues. Not the least of which, for me, is suddenly finding yourself in the very odd position of moving to knowing that people you’ve considered part of your work life for years and years are no longer “we.”
 [Editor’s note: Neither the author nor anyone associated with this blog is a lawyer of any kind. This blog is not to be taken for legal advice under any circumstances. If you have a personal privacy question of law, consult a trained and licensed attorney.]
[Editor’s note: Neither the author nor anyone associated with this blog is a lawyer of any kind. This blog is not to be taken for legal advice under any circumstances. If you have a personal privacy question of law, consult a trained and licensed attorney.]